
Stop Losing Lead Conversions
Stop Losing Lead Conversions
Are you losing leads & lead conversions due to various reasons like missed follow-ups, failed automation & many other reasons?
Here is the perfect solution.













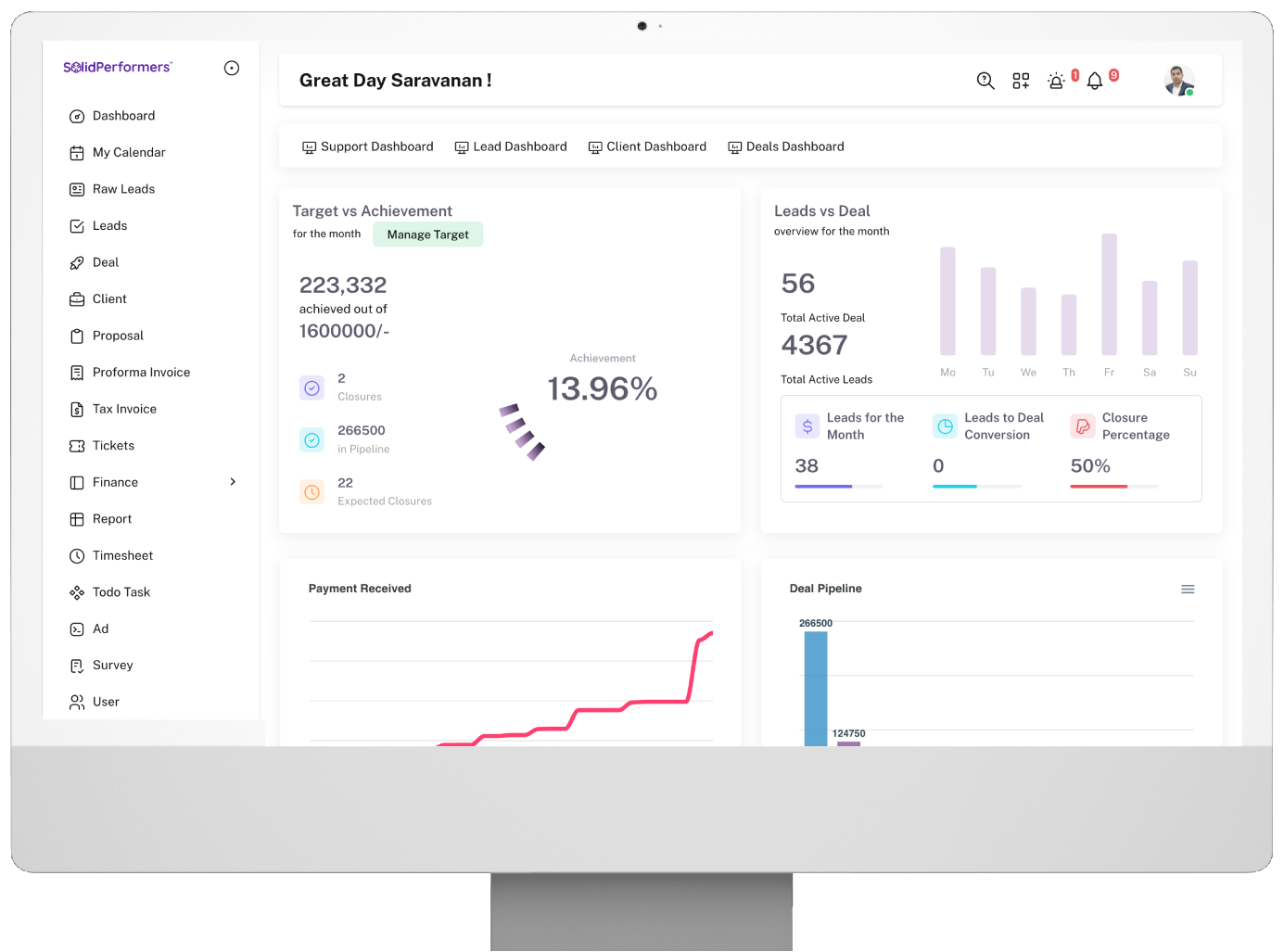


Interact with our Business Consultants & understand the importance of using CRM in a much better way.